security
-
 The World’s First Hacking-preventing Cryptographic Semiconductor Chip
With the dramatic increase in the amount of information exchanged between components or devices in the 5G/6G era, such as for the Internet of Things (IoT) and autonomous driving, hacking attacks are becoming more sophisticated. Consequently, enhancing security functions is essential for safely transmitting data between and among devices.
On February 29th, a KAIST research team led by Professors Yang-gyu Choi and Seung-tak Ryu from the School of Electrical Engineering announced the successful development of the world's first security cryptographic semiconductor.
The team has developed the Cryptoristor, a cryptographic transistor based on FinFET technology, produced through a 100% silicon-compatible process, for the first time in the world. Cryptoristor is a random number generator (RNG) with unparalleled characteristics, featuring a unique structure comprising a single transistor and a distinctive mechanism.
In all security environments, including artificial intelligence, the most crucial element is the RNG. In the most commonly used security chip, the Advanced Encryption Standard (AES), the RNG is a core component, occupying approximately 75% of the total chip area and more than 85% of its energy consumption. Hence, there is an urgent need for the development of low-power/ultra-small RNGs suitable for mobile or IoT devices.
Existing RNGs come with limitations as they lack compatibility with silicon CMOS processes and circuit-based RNGs occupy a large surface area.
In contrast, the team’s newly developed Cryptoristor, a cryptographic semiconductor based on a single-component structure, consumes and occupies less than .001 of the power and area compared to the current chips being used. Utilizing the inherent randomness of FinFETs, fabricated on a Silicon-on-Insulator (SOI) substrate with an insulating layer formed beneath the silicon, the team developed an RNG that unpredictably produces zeroes and ones.
< Figure 1. Conceptual diagram of the security cryptographic transistor device. >
Generally speaking, preventing hackers from predicting the encrypted algorithms during data exchanges through mobile devices is pivotal. Therefore, this method ensures unpredictability by generating random sequences of zeroes and ones that change every time.
Moreover, while the Cryptoristor-based RNG research is the world's first of its kind without any international implementation cases, it shares the same transistor structure as existing logic or memory components. This enables 100% production through rapid mass production processes using existing semiconductor facilities at a low cost.
Seung-il Kim, a PhD student who led the research, explained the significance of the study, stating, "As a cryptographic semiconductor, the ultra-small/low-power random number generator enhances security through its distinctive unpredictability, supporting safe hyperconnectivity with secure transmissions between chips or devices. Particularly, compared to previous research, it offers excellent advantages in terms of energy consumption, integration density, and cost, making it suitable for IoT device environments."
This research, with master’s student Hyung-jin Yoo as the co-author, was officially published in the online edition of Science Advances, a sister journal of Science, in February 2024 (research paper title: Cryptographic transistor for true random number generator with low power consumption).
This research received support from the Next-Generation Intelligent Semiconductor Technology Development Project and the Core Technology Development Project for the National Semiconductor Research Laboratory.
2024.03.07 View 8798
The World’s First Hacking-preventing Cryptographic Semiconductor Chip
With the dramatic increase in the amount of information exchanged between components or devices in the 5G/6G era, such as for the Internet of Things (IoT) and autonomous driving, hacking attacks are becoming more sophisticated. Consequently, enhancing security functions is essential for safely transmitting data between and among devices.
On February 29th, a KAIST research team led by Professors Yang-gyu Choi and Seung-tak Ryu from the School of Electrical Engineering announced the successful development of the world's first security cryptographic semiconductor.
The team has developed the Cryptoristor, a cryptographic transistor based on FinFET technology, produced through a 100% silicon-compatible process, for the first time in the world. Cryptoristor is a random number generator (RNG) with unparalleled characteristics, featuring a unique structure comprising a single transistor and a distinctive mechanism.
In all security environments, including artificial intelligence, the most crucial element is the RNG. In the most commonly used security chip, the Advanced Encryption Standard (AES), the RNG is a core component, occupying approximately 75% of the total chip area and more than 85% of its energy consumption. Hence, there is an urgent need for the development of low-power/ultra-small RNGs suitable for mobile or IoT devices.
Existing RNGs come with limitations as they lack compatibility with silicon CMOS processes and circuit-based RNGs occupy a large surface area.
In contrast, the team’s newly developed Cryptoristor, a cryptographic semiconductor based on a single-component structure, consumes and occupies less than .001 of the power and area compared to the current chips being used. Utilizing the inherent randomness of FinFETs, fabricated on a Silicon-on-Insulator (SOI) substrate with an insulating layer formed beneath the silicon, the team developed an RNG that unpredictably produces zeroes and ones.
< Figure 1. Conceptual diagram of the security cryptographic transistor device. >
Generally speaking, preventing hackers from predicting the encrypted algorithms during data exchanges through mobile devices is pivotal. Therefore, this method ensures unpredictability by generating random sequences of zeroes and ones that change every time.
Moreover, while the Cryptoristor-based RNG research is the world's first of its kind without any international implementation cases, it shares the same transistor structure as existing logic or memory components. This enables 100% production through rapid mass production processes using existing semiconductor facilities at a low cost.
Seung-il Kim, a PhD student who led the research, explained the significance of the study, stating, "As a cryptographic semiconductor, the ultra-small/low-power random number generator enhances security through its distinctive unpredictability, supporting safe hyperconnectivity with secure transmissions between chips or devices. Particularly, compared to previous research, it offers excellent advantages in terms of energy consumption, integration density, and cost, making it suitable for IoT device environments."
This research, with master’s student Hyung-jin Yoo as the co-author, was officially published in the online edition of Science Advances, a sister journal of Science, in February 2024 (research paper title: Cryptographic transistor for true random number generator with low power consumption).
This research received support from the Next-Generation Intelligent Semiconductor Technology Development Project and the Core Technology Development Project for the National Semiconductor Research Laboratory.
2024.03.07 View 8798 -
 Professor Sang Kil Cha Receives IEEE Test-of-Time Award
Professor Sang Kil Cha from the Graduate School of Information Security (GSIS) in the School of Computing received the Test-of-Time Award from IEEE Security & Privacy, a top conference in the field of information security.
The Test-of-Time Award recognizes the research papers that have influenced the field of information security the most over the past decade. Three papers were selected this year, and Professor Cha is the first Korean winner of the award.
The paper by Professor Cha was published in 2012 under the title, “Unleashing Mayhem on Binary Code”. It was the first to ever suggest an algorithm that automatically finds bugs in binary code and creates exploits that links them to an attack code.
The developed algorithm is a core technique used for world-class cyber security hacking competitions like the Cyber Grand Challenge, an AI hacking contest.
Starting with this research, Professor Cha has carried out various studies to develop technologies that can find bugs and vulnerabilities through binary analyses, and is currently developing B2R2, a Korean platform that can analyze various binary codes.
2022.06.13 View 6290
Professor Sang Kil Cha Receives IEEE Test-of-Time Award
Professor Sang Kil Cha from the Graduate School of Information Security (GSIS) in the School of Computing received the Test-of-Time Award from IEEE Security & Privacy, a top conference in the field of information security.
The Test-of-Time Award recognizes the research papers that have influenced the field of information security the most over the past decade. Three papers were selected this year, and Professor Cha is the first Korean winner of the award.
The paper by Professor Cha was published in 2012 under the title, “Unleashing Mayhem on Binary Code”. It was the first to ever suggest an algorithm that automatically finds bugs in binary code and creates exploits that links them to an attack code.
The developed algorithm is a core technique used for world-class cyber security hacking competitions like the Cyber Grand Challenge, an AI hacking contest.
Starting with this research, Professor Cha has carried out various studies to develop technologies that can find bugs and vulnerabilities through binary analyses, and is currently developing B2R2, a Korean platform that can analyze various binary codes.
2022.06.13 View 6290 -
 Team Geumo Wins Consecutive Victories in K-Cyber Security Challenge
< Professor Sang Kil Cha >
< Masters Candidate Kangsu Kim and Researcher Corentin Soulet >
Team Geumo, led by Professor Sang Kil Cha from the Graduate School of Information Security, won the K-Cyber Security Challenge in the AI-based automatic vulnerability detection division for two consecutive years in 2018 and 2019.
The K-Cyber Security Challenge is an inter-machine hacking competition. Participants develop and operate AI-based systems that are capable of independently identifying software vulnerabilities and gaining operating rights through hacking. The K-Cyber Security Challenge, inspired by the US Cyber Grand Challenge launched by the Defense Advanced Research Projects Agency (DARPA), is hosted by the Ministry of Science and ICT and organized by the Korea Internet and Security Agency.
Researcher Corentin Soulet of the School of Computing and master’s student Kangsu Kim of the Graduate School of Information Security teamed up for the competition. Professor Cha, who has led the research on software and systems security since his days at Carnegie Mellon University, succeeded in establishing a world-class system using domestic technology.
In a recent collaboration with the Cyber Security Research Center, Professor Cha achieved a ten-fold increase in the speed of binary analysis engines, a key component of AI-based hacking systems. For this accomplishment, he received the Best Paper Award at the 2019 Network and Distributed System Security Workshop on Binary Analysis Research (NDSS BAR).
Kangsu Kim said, "It is a great honor to win the competition two years in a row. I will continue to work hard and apply my knowledge to serve society.”
(END)
2019.12.20 View 11422
Team Geumo Wins Consecutive Victories in K-Cyber Security Challenge
< Professor Sang Kil Cha >
< Masters Candidate Kangsu Kim and Researcher Corentin Soulet >
Team Geumo, led by Professor Sang Kil Cha from the Graduate School of Information Security, won the K-Cyber Security Challenge in the AI-based automatic vulnerability detection division for two consecutive years in 2018 and 2019.
The K-Cyber Security Challenge is an inter-machine hacking competition. Participants develop and operate AI-based systems that are capable of independently identifying software vulnerabilities and gaining operating rights through hacking. The K-Cyber Security Challenge, inspired by the US Cyber Grand Challenge launched by the Defense Advanced Research Projects Agency (DARPA), is hosted by the Ministry of Science and ICT and organized by the Korea Internet and Security Agency.
Researcher Corentin Soulet of the School of Computing and master’s student Kangsu Kim of the Graduate School of Information Security teamed up for the competition. Professor Cha, who has led the research on software and systems security since his days at Carnegie Mellon University, succeeded in establishing a world-class system using domestic technology.
In a recent collaboration with the Cyber Security Research Center, Professor Cha achieved a ten-fold increase in the speed of binary analysis engines, a key component of AI-based hacking systems. For this accomplishment, he received the Best Paper Award at the 2019 Network and Distributed System Security Workshop on Binary Analysis Research (NDSS BAR).
Kangsu Kim said, "It is a great honor to win the competition two years in a row. I will continue to work hard and apply my knowledge to serve society.”
(END)
2019.12.20 View 11422 -
 Anti-drone Technology for Anti-Terrorism Applications
(from top right clockwise: Professor Yongdae Kim,
PhD Candidates Yujin Kwon, Juhwan Noh, Hocheol Shin, and Dohyun Kim)
KAIST researchers have developed anti-drone technology that can hijack other drones by spoofing its location using fake GPS signals. This technology can safely guide a drone to a desired location without any sudden change in direction in emergency situations, and thus respond effectively to dangerous drones such as those intending to carry out acts of terrorism.
Advancements in the drone industry have led to the wider use of drones in our daily lives in areas of reconnaissance, searching and rescuing, disaster prevention and response, and delivery services. At the same time, there has also been a growing concern about privacy, safety, and security issues regarding drones, especially those arising from intrusion into private property and secure facilities. Therefore, the anti-drone industry is rapidly expanding to detect and respond to this possible drone invasion.
The current anti-drone systems used in airports and other key locations utilize electronic jamming signals, high-power lasers, or nets to neutralize drones. For example, drones trespassing on airports are often countered with simple jamming signals that can prevent the drones from moving and changing position, but this may result in a prolonged delay in flight departures and arrivals at the airports. Drones used for terrorist attacks – armed with explosives or weapons – must also be neutralized a safe distance from the public and vital infrastructure to minimize any damage.
Due to this need for a new anti-drone technology to counter these threats, a KAIST research team led by Professor Yongdae Kim from the School of Electrical Engineering has developed technology that securely thwarts drones by tricking them with fake GPS signals.
Fake GPS signals have been used in previous studies to cause confusion inside the drone regarding its location, making the drone drift from its position or path. However, such attack tactics cannot be applied in GPS safety mode. GPS safety mode is an emergency mode that ensures drone safety when the signal is cut or location accuracy is low due to a fake GPS signals. This mode differs between models and manufacturers.
Professor Kim’s team analyzed the GPS safety mode of different drone models made from major drone manufacturers such as DJI and Parrot, made classification systems, and designed a drone abduction technique that covers almost all the types of drone GPS safety modes, and is universally applicable to any drone that uses GPS regardless of model or manufacturer. The research team applied their new technique to four different drones and have proven that the drones can be safely hijacked and guided to the direction of intentional abduction within a small margin of error.
Professor Kim said, “Conventional consumer drones equipped with GPS safety mode seem to be safe from fake GPS signals, however, most of these drones are able to be detoured since they detect GPS errors in a rudimentary manner.” He continued, “This technology can contribute particularly to reducing damage to airports and the airline industry caused by illegal drone flights.”
The research team is planning to commercialize the developed technology by applying it to existing anti-drone solutions through technology transfer.” This research, featured in the ACM Transactions on Privacy and Security (TOPS) on April 9, was supported by the Defense Acquisition Program Administration (DAPA) and the Agency for Defense Development (ADD).
Image 1.
Experimental environment in which a fake GPS signal was produced from a PC and injected into the drone signal using directional antennae
Publication:
Juhwan Noh, Yujin Kwon, Yunmok Son, Hocheol Shin, Dohyun Kim, Jaeyeong Choi, and Yongdae Kim. 2019. Tractor Beam: Safe-hijacking of Consumer Drones with Adaptive GPS Spoofing. ACM Transactions on Privacy and Security. New York, NY, USA, Vol. 22, No. 2, Article 12, 26 pages. https://doi.org/10.1145/3309735
Profile: Prof. Yongdae Kim, MS, PhD
yongdaek@kaist.ac.kr
https://www.syssec.kr/
Professor
School of Electrical Engineering
Korea Advanced Institute of Science and Technology (KAIST)
http://kaist.ac.kr Daejeon 34141, Korea
Profile: Juhwan Noh, PhD Candidate
juhwan@kaist.ac.kr
PhD Candidate
System Security (SysSec) Lab
School of Electrical Engineering
Korea Advanced Institute of Science and Technology (KAIST)
http://kaist.ac.kr Daejeon 34141, Korea
(END)
2019.06.25 View 45338
Anti-drone Technology for Anti-Terrorism Applications
(from top right clockwise: Professor Yongdae Kim,
PhD Candidates Yujin Kwon, Juhwan Noh, Hocheol Shin, and Dohyun Kim)
KAIST researchers have developed anti-drone technology that can hijack other drones by spoofing its location using fake GPS signals. This technology can safely guide a drone to a desired location without any sudden change in direction in emergency situations, and thus respond effectively to dangerous drones such as those intending to carry out acts of terrorism.
Advancements in the drone industry have led to the wider use of drones in our daily lives in areas of reconnaissance, searching and rescuing, disaster prevention and response, and delivery services. At the same time, there has also been a growing concern about privacy, safety, and security issues regarding drones, especially those arising from intrusion into private property and secure facilities. Therefore, the anti-drone industry is rapidly expanding to detect and respond to this possible drone invasion.
The current anti-drone systems used in airports and other key locations utilize electronic jamming signals, high-power lasers, or nets to neutralize drones. For example, drones trespassing on airports are often countered with simple jamming signals that can prevent the drones from moving and changing position, but this may result in a prolonged delay in flight departures and arrivals at the airports. Drones used for terrorist attacks – armed with explosives or weapons – must also be neutralized a safe distance from the public and vital infrastructure to minimize any damage.
Due to this need for a new anti-drone technology to counter these threats, a KAIST research team led by Professor Yongdae Kim from the School of Electrical Engineering has developed technology that securely thwarts drones by tricking them with fake GPS signals.
Fake GPS signals have been used in previous studies to cause confusion inside the drone regarding its location, making the drone drift from its position or path. However, such attack tactics cannot be applied in GPS safety mode. GPS safety mode is an emergency mode that ensures drone safety when the signal is cut or location accuracy is low due to a fake GPS signals. This mode differs between models and manufacturers.
Professor Kim’s team analyzed the GPS safety mode of different drone models made from major drone manufacturers such as DJI and Parrot, made classification systems, and designed a drone abduction technique that covers almost all the types of drone GPS safety modes, and is universally applicable to any drone that uses GPS regardless of model or manufacturer. The research team applied their new technique to four different drones and have proven that the drones can be safely hijacked and guided to the direction of intentional abduction within a small margin of error.
Professor Kim said, “Conventional consumer drones equipped with GPS safety mode seem to be safe from fake GPS signals, however, most of these drones are able to be detoured since they detect GPS errors in a rudimentary manner.” He continued, “This technology can contribute particularly to reducing damage to airports and the airline industry caused by illegal drone flights.”
The research team is planning to commercialize the developed technology by applying it to existing anti-drone solutions through technology transfer.” This research, featured in the ACM Transactions on Privacy and Security (TOPS) on April 9, was supported by the Defense Acquisition Program Administration (DAPA) and the Agency for Defense Development (ADD).
Image 1.
Experimental environment in which a fake GPS signal was produced from a PC and injected into the drone signal using directional antennae
Publication:
Juhwan Noh, Yujin Kwon, Yunmok Son, Hocheol Shin, Dohyun Kim, Jaeyeong Choi, and Yongdae Kim. 2019. Tractor Beam: Safe-hijacking of Consumer Drones with Adaptive GPS Spoofing. ACM Transactions on Privacy and Security. New York, NY, USA, Vol. 22, No. 2, Article 12, 26 pages. https://doi.org/10.1145/3309735
Profile: Prof. Yongdae Kim, MS, PhD
yongdaek@kaist.ac.kr
https://www.syssec.kr/
Professor
School of Electrical Engineering
Korea Advanced Institute of Science and Technology (KAIST)
http://kaist.ac.kr Daejeon 34141, Korea
Profile: Juhwan Noh, PhD Candidate
juhwan@kaist.ac.kr
PhD Candidate
System Security (SysSec) Lab
School of Electrical Engineering
Korea Advanced Institute of Science and Technology (KAIST)
http://kaist.ac.kr Daejeon 34141, Korea
(END)
2019.06.25 View 45338 -
 KAIST Shows Strong Performance in Crypto Contest Korea 2018
(Awardees at the ceremony for Crypto Contest Korea 2018)
A paper titled “Indifferentiability of Truncated Random Permutations” by PhD candidate Wonseok Choi and MS candidate Byeonghak Lee (under Professor Jooyoung Lee) from the KAIST Graduate School of Information Security (GSIS) won first place in Crypto Contest Korea 2018. Byeonghak Lee became a repeat winner since his paper titled “Tweakable Block Ciphers Secure Beyond the Birthday Bound in the Ideal Cipher Model” also received an award at Crypto Contest Korea 2017.
The contest, hosted by the Korea Cryptography Forum, the Korea Institute of Information Security & Cryptology, and the National Security Research Institute and sponsored by the National Intelligence Service, was held for promoting cryptography in Korea. The total prize money is fifty million won with ten million won going to the first place winners.
The contest was divided into three divisions: paper, problem solving, and idea. Among the three divisions, first place came from the paper division only.
Besides first place, KAIST students showed outstanding performance in the contest. PhD candidate Seongkwang Kim received participation prize while he also received special prizes with MS candidate Yeongmin Lee. The hacking club GoN (under Professor Sang Kil Cha), comprised of undergraduate students from the GSIS was awarded the grand prize in the division of problem solving.
The award ceremony was held during the Future Crypto Workshop 2018 on November 15. The awards ceremony for Crypto Expert Korea 2018 were also held there, and PhD candidate Ji-Eun Lee from the School of Computing and Byeonghak Lee received awards, the grand prize and runner-up prize respectively.
2018.11.27 View 9839
KAIST Shows Strong Performance in Crypto Contest Korea 2018
(Awardees at the ceremony for Crypto Contest Korea 2018)
A paper titled “Indifferentiability of Truncated Random Permutations” by PhD candidate Wonseok Choi and MS candidate Byeonghak Lee (under Professor Jooyoung Lee) from the KAIST Graduate School of Information Security (GSIS) won first place in Crypto Contest Korea 2018. Byeonghak Lee became a repeat winner since his paper titled “Tweakable Block Ciphers Secure Beyond the Birthday Bound in the Ideal Cipher Model” also received an award at Crypto Contest Korea 2017.
The contest, hosted by the Korea Cryptography Forum, the Korea Institute of Information Security & Cryptology, and the National Security Research Institute and sponsored by the National Intelligence Service, was held for promoting cryptography in Korea. The total prize money is fifty million won with ten million won going to the first place winners.
The contest was divided into three divisions: paper, problem solving, and idea. Among the three divisions, first place came from the paper division only.
Besides first place, KAIST students showed outstanding performance in the contest. PhD candidate Seongkwang Kim received participation prize while he also received special prizes with MS candidate Yeongmin Lee. The hacking club GoN (under Professor Sang Kil Cha), comprised of undergraduate students from the GSIS was awarded the grand prize in the division of problem solving.
The award ceremony was held during the Future Crypto Workshop 2018 on November 15. The awards ceremony for Crypto Expert Korea 2018 were also held there, and PhD candidate Ji-Eun Lee from the School of Computing and Byeonghak Lee received awards, the grand prize and runner-up prize respectively.
2018.11.27 View 9839 -
 MoU Signed by the Republic of Korea Army and KAIST
(From left: KAIST President Sung-Chul Shin and ROKA Chief of Staff Youngwoo Kim)
On March 7, the Republic of Korea Army (ROKA) and KAIST signed an MoU and opened special sessions dedicated to the army in order to reinforce research and development capacities.
The close partnership between KAIST and ROKA will provide an opportunity to establish advanced combat development systems.
Through the MoU, signed by KAIST President Sung-Chul Shin and ROKA Chief of Staff Youngwoo Kim, both organizations will discuss new opportunities for cooperation between academia and military and establish an institute and its curriculum.
KAIST is offering special sessions for the army March 5-9, where about 150 executives from ROKA, including the headquarters, education and training command, and logistics command, will participate.
These session are expected to enhance the army’s capabilities through education on cutting-edge equipment that will emerge during the Fourth Industrial Revolution.
The director of the KAIST Security Convergence Institute, Soo Hyun Kim, said, “KAIST and ROKA will plan and operate various programs together though this partnership as well as special sessions. I hope this cooperation will be an opportunity to enhance the combat development of ROKA.”
2018.03.07 View 7161
MoU Signed by the Republic of Korea Army and KAIST
(From left: KAIST President Sung-Chul Shin and ROKA Chief of Staff Youngwoo Kim)
On March 7, the Republic of Korea Army (ROKA) and KAIST signed an MoU and opened special sessions dedicated to the army in order to reinforce research and development capacities.
The close partnership between KAIST and ROKA will provide an opportunity to establish advanced combat development systems.
Through the MoU, signed by KAIST President Sung-Chul Shin and ROKA Chief of Staff Youngwoo Kim, both organizations will discuss new opportunities for cooperation between academia and military and establish an institute and its curriculum.
KAIST is offering special sessions for the army March 5-9, where about 150 executives from ROKA, including the headquarters, education and training command, and logistics command, will participate.
These session are expected to enhance the army’s capabilities through education on cutting-edge equipment that will emerge during the Fourth Industrial Revolution.
The director of the KAIST Security Convergence Institute, Soo Hyun Kim, said, “KAIST and ROKA will plan and operate various programs together though this partnership as well as special sessions. I hope this cooperation will be an opportunity to enhance the combat development of ROKA.”
2018.03.07 View 7161 -
 KAIST International Community Celebrates the Year-End
KAIST international community all gathered in celebration of the year-end on December 5 at the KAIST auditorium. This year, the community made the year-end party very special, expressing their appreciation very touching way at the event hosted by the International Scholar and Student Services (ISSS). Nearly 650 international faculty, students, and their family members joined the party.
Currently, 184 faculty members and researchers from 29 countries are working at KAIST, with 901 international students from 92 countries enrolled.
The two-hour party offered them a chance to enjoy a wide variety of activities and events, including dance performances, student performances, games, and dinner.
The party also had a meaningful award ceremony. Prior to the event, a month-long survey was conducted, asking international scholars and students which on-campus team they were most thankful for this year. Candidates for the appreciation award were: Safety and Security Team, Student Affairs Team, Campus Police, dormitory supervisors, and campus cleaning staff.
Approximately 470 scholars and students responded to the survey and 214 voted for the campus cleaning staff (45.5%).
(President Sung-Chul Shin and Myeongja Kim)
Ms. Myeongja Kim, a director of the cleaning staff in the undergraduate zone, received the award on behalf of the entire cleaning staff. At the ceremony, President Sung-Chul Shin conferred the award.
President Shin in his welcoming remarks said that globalization is his priority and urgent mission. To make KAIST more globalized, he said he will focus on three agendas; to make the campus KAIST a more welcoming environment for international community; to make campus more inclusive and diverse; to enhance the global visibility of KAIST more proactively. Click for the full text of opening remarks
2017.12.11 View 6616
KAIST International Community Celebrates the Year-End
KAIST international community all gathered in celebration of the year-end on December 5 at the KAIST auditorium. This year, the community made the year-end party very special, expressing their appreciation very touching way at the event hosted by the International Scholar and Student Services (ISSS). Nearly 650 international faculty, students, and their family members joined the party.
Currently, 184 faculty members and researchers from 29 countries are working at KAIST, with 901 international students from 92 countries enrolled.
The two-hour party offered them a chance to enjoy a wide variety of activities and events, including dance performances, student performances, games, and dinner.
The party also had a meaningful award ceremony. Prior to the event, a month-long survey was conducted, asking international scholars and students which on-campus team they were most thankful for this year. Candidates for the appreciation award were: Safety and Security Team, Student Affairs Team, Campus Police, dormitory supervisors, and campus cleaning staff.
Approximately 470 scholars and students responded to the survey and 214 voted for the campus cleaning staff (45.5%).
(President Sung-Chul Shin and Myeongja Kim)
Ms. Myeongja Kim, a director of the cleaning staff in the undergraduate zone, received the award on behalf of the entire cleaning staff. At the ceremony, President Sung-Chul Shin conferred the award.
President Shin in his welcoming remarks said that globalization is his priority and urgent mission. To make KAIST more globalized, he said he will focus on three agendas; to make the campus KAIST a more welcoming environment for international community; to make campus more inclusive and diverse; to enhance the global visibility of KAIST more proactively. Click for the full text of opening remarks
2017.12.11 View 6616 -
 KAIST Partners with Technion and Hyundai Motors for Future Mobility Technology Development
(KAIST Associate Vice President of Research Joung-Ho Kim(third from left) poses with Technion President Pereta Lavie and CTO Tae Won Im of Hyundai Motors)
KAIST has partnered with the Israel Institute of Technology, Technion, and Hyundai Motors to take the lead in the field of future mobility technologies. The three parties signed a consortium of global alliance for future mobility partnership at Technion on Sept. 5. KAIST Associate Vice President of Research Kim Joung-Ho, Hyundai Motor’s Central Advanced Research and Engineering CTO Tae Won Lim, and Technion President Peretz Lavie signed the MOU.
The three parties agreed to conduct joint research on hi-tech mobility areas including self-driving systems, cyber security, and AI in mobility. With the signing of the consortium, KAIST's technology in AI, semiconductors, and autonomous cars will produce synergy with Technion’s connected car solutions, advancing Hyundai Motor's competitiveness in the future mobility market.
In addition to the consortium, the three parties will set-up a startup consulting committee, which will provide consulting services for nurturing venture startups with creative ideas and outstanding technological prowess in their host countries.
2017.09.07 View 7242
KAIST Partners with Technion and Hyundai Motors for Future Mobility Technology Development
(KAIST Associate Vice President of Research Joung-Ho Kim(third from left) poses with Technion President Pereta Lavie and CTO Tae Won Im of Hyundai Motors)
KAIST has partnered with the Israel Institute of Technology, Technion, and Hyundai Motors to take the lead in the field of future mobility technologies. The three parties signed a consortium of global alliance for future mobility partnership at Technion on Sept. 5. KAIST Associate Vice President of Research Kim Joung-Ho, Hyundai Motor’s Central Advanced Research and Engineering CTO Tae Won Lim, and Technion President Peretz Lavie signed the MOU.
The three parties agreed to conduct joint research on hi-tech mobility areas including self-driving systems, cyber security, and AI in mobility. With the signing of the consortium, KAIST's technology in AI, semiconductors, and autonomous cars will produce synergy with Technion’s connected car solutions, advancing Hyundai Motor's competitiveness in the future mobility market.
In addition to the consortium, the three parties will set-up a startup consulting committee, which will provide consulting services for nurturing venture startups with creative ideas and outstanding technological prowess in their host countries.
2017.09.07 View 7242 -
 Professor Kwangjo Kim Named as Fellow of IACR
Professor Kwangjo Kim of the Graduate School of Information Security has been selected as a fellow of the International Association for Cryptologic Research (IACR).
The IACR has honored outstanding scholars who have achieved academic excellence in cryptologic research since 2004. He is the first Korean scholar to receive an IACR fellowship.
The IACR, established in 1981, is responsible for organizing international cryptologic conferences every year including the three major cryptologic academic conferences Eurocrypt, Crypto, and Asiacript. The IACR also sponsors workshop series such as the Theory of Cryptography Conference (TCC), the Workshop on Fast Software Encryption (FSE), the Public Key Cryptography Workshop (PKC), and Cryptographic Hardware and Embedded Systems (CHES).
Professor Kim, an internationally acclaimed scholar in the fields of cryptology and information security theory and its applications, was recognized for his outstanding academic achievements and leadership. He has made significant contributions to cryptology in Korea by hosting Asiacript in 1996 and 2001 as well as CHES in 2014. During his 34 years of academic activities, he has published more than 80 SCI journal papers and garnered more than 20,000 citations.
Professor Kim served on the board of the directors of the IACR from 2000 to 2004 and was the chairperson of the Asiacript Steering Committee from 2005 to 2008. He is on the editorial board of the online journal Cryptography.
Professor Kim said, “I am so humbled and honored to be named as a fellow of such a prestigious academic association. I will continue to strive to assist highly educated information security personnel with further research in cryptology.”
2017.03.16 View 9728
Professor Kwangjo Kim Named as Fellow of IACR
Professor Kwangjo Kim of the Graduate School of Information Security has been selected as a fellow of the International Association for Cryptologic Research (IACR).
The IACR has honored outstanding scholars who have achieved academic excellence in cryptologic research since 2004. He is the first Korean scholar to receive an IACR fellowship.
The IACR, established in 1981, is responsible for organizing international cryptologic conferences every year including the three major cryptologic academic conferences Eurocrypt, Crypto, and Asiacript. The IACR also sponsors workshop series such as the Theory of Cryptography Conference (TCC), the Workshop on Fast Software Encryption (FSE), the Public Key Cryptography Workshop (PKC), and Cryptographic Hardware and Embedded Systems (CHES).
Professor Kim, an internationally acclaimed scholar in the fields of cryptology and information security theory and its applications, was recognized for his outstanding academic achievements and leadership. He has made significant contributions to cryptology in Korea by hosting Asiacript in 1996 and 2001 as well as CHES in 2014. During his 34 years of academic activities, he has published more than 80 SCI journal papers and garnered more than 20,000 citations.
Professor Kim served on the board of the directors of the IACR from 2000 to 2004 and was the chairperson of the Asiacript Steering Committee from 2005 to 2008. He is on the editorial board of the online journal Cryptography.
Professor Kim said, “I am so humbled and honored to be named as a fellow of such a prestigious academic association. I will continue to strive to assist highly educated information security personnel with further research in cryptology.”
2017.03.16 View 9728 -
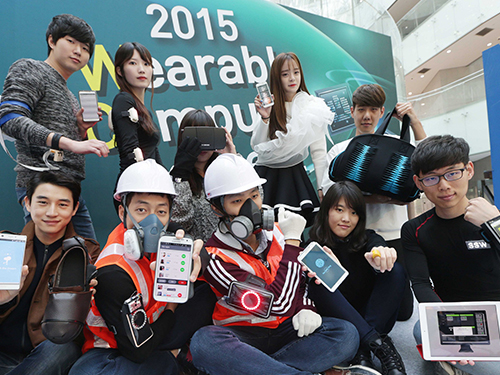 KAIST Hosts the Wearable Computer Contest 2015
“What you see is a compact electronic system on a dust mask, which monitors the amount of dust taken in by a worker and lets other workers know if the person is injured in an industrial site,” said Bum Taek Jung, a Master’s candidate from Sungkyunkwan University during the Wearable Computer Contest 2015 held in KI building of KAIST on November 5, 2015.
He explained his interest in developing this system, “Dust-related respiratory diseases and falling accidents are still prevalent in industrial sites.” He added, “Using the smart dust mask helps monitoring workers’ physical condition in real time, allowing us to cope with accidents in a much more timely manner.” A smart dust mask is a portable device that alerts the user with orange or red light signs when the amount of dust inhaled by the user is higher than the threshold. Its application on a smartphone can also allow project managers to alert the risk of falling accidents to workers by employing a gyroscope and an accelerometer on the mask.
The Wearable Computer Contest 2015 met for the eleventh time at KAIST on November 5-6, 2015. A wearable computer refers to a portable device which users can wear directly on the body or on their clothes while moving. Products that can provide various services by connecting to a smartphone have become increasingly popular. The contest is an excellent opportunity for university students to design creative wearable systems similar to those often depicted in movies and comics.
This year 102 teams from universities all over the nation participated. After screening and evaluation of their presentations, only 8 teams in the product section and 3 teams in the ideas section were selected for the finals. Of the many entries to the contest, the ECG security system caught many people’s attention. The wearable, which attaches to a shirt, acts like an electrocardiogram. By comparing the ECG reading with the one stored in the data server, the wearable can authenticate the user. The system could be widely used by enterprises and financial companies where tight security and authentication are crucial.
The winners of the product and the ideas sections received USD 4,300 and usd 860 respectively along with Minister Prizes from the Minister of Science, ICT and Future Planning of Korea. The Chairman of the contest, Professor Hoi-Jun Yoo from the Electrical Engineering Department of KAIST said, “The contest will be a great opportunity for anyone to have a look at advanced wearable devices developed through close integration of state-of-the-art technologies and creative ideas from young minds.”
2015.11.05 View 9505
KAIST Hosts the Wearable Computer Contest 2015
“What you see is a compact electronic system on a dust mask, which monitors the amount of dust taken in by a worker and lets other workers know if the person is injured in an industrial site,” said Bum Taek Jung, a Master’s candidate from Sungkyunkwan University during the Wearable Computer Contest 2015 held in KI building of KAIST on November 5, 2015.
He explained his interest in developing this system, “Dust-related respiratory diseases and falling accidents are still prevalent in industrial sites.” He added, “Using the smart dust mask helps monitoring workers’ physical condition in real time, allowing us to cope with accidents in a much more timely manner.” A smart dust mask is a portable device that alerts the user with orange or red light signs when the amount of dust inhaled by the user is higher than the threshold. Its application on a smartphone can also allow project managers to alert the risk of falling accidents to workers by employing a gyroscope and an accelerometer on the mask.
The Wearable Computer Contest 2015 met for the eleventh time at KAIST on November 5-6, 2015. A wearable computer refers to a portable device which users can wear directly on the body or on their clothes while moving. Products that can provide various services by connecting to a smartphone have become increasingly popular. The contest is an excellent opportunity for university students to design creative wearable systems similar to those often depicted in movies and comics.
This year 102 teams from universities all over the nation participated. After screening and evaluation of their presentations, only 8 teams in the product section and 3 teams in the ideas section were selected for the finals. Of the many entries to the contest, the ECG security system caught many people’s attention. The wearable, which attaches to a shirt, acts like an electrocardiogram. By comparing the ECG reading with the one stored in the data server, the wearable can authenticate the user. The system could be widely used by enterprises and financial companies where tight security and authentication are crucial.
The winners of the product and the ideas sections received USD 4,300 and usd 860 respectively along with Minister Prizes from the Minister of Science, ICT and Future Planning of Korea. The Chairman of the contest, Professor Hoi-Jun Yoo from the Electrical Engineering Department of KAIST said, “The contest will be a great opportunity for anyone to have a look at advanced wearable devices developed through close integration of state-of-the-art technologies and creative ideas from young minds.”
2015.11.05 View 9505 -
 KAIST and Oberthur Technologies Agree for Research and Development in Mobile Security
Professor Kwangjo Kim of the School of Computing at KAIST has signed a research and development (R&D) agreement with Marc Bertin, the Chief Technology Officer of Oberthur Technologies (OT), a French security solutions firm, on September 18, 2015 in Paris.
Under the agreement, KAIST and OT will conduct joint research on mobile security as well as implement an internship program for KAIST graduate students to work either at OT’s R&D center in Korea or in France.
OT has established a research center in Korea in July 2014, which was the fourth of its research centers in Asia.
Professor Kim said, “Our goal at KAIST is to cultivate top-level security experts in security technologies. By partnering with such a leader in security technologies as OT, we know that we will both help shape tomorrow’s security solution for the IoT (Internet of Things) space.”
In the picture, Professor Kwangjo Kim (left) shakes hands with Marc Bertin, the Chief Technology Officer of Oberthur Technologies (right), after the signing of a memorandum of understanding.
2015.09.24 View 8654
KAIST and Oberthur Technologies Agree for Research and Development in Mobile Security
Professor Kwangjo Kim of the School of Computing at KAIST has signed a research and development (R&D) agreement with Marc Bertin, the Chief Technology Officer of Oberthur Technologies (OT), a French security solutions firm, on September 18, 2015 in Paris.
Under the agreement, KAIST and OT will conduct joint research on mobile security as well as implement an internship program for KAIST graduate students to work either at OT’s R&D center in Korea or in France.
OT has established a research center in Korea in July 2014, which was the fourth of its research centers in Asia.
Professor Kim said, “Our goal at KAIST is to cultivate top-level security experts in security technologies. By partnering with such a leader in security technologies as OT, we know that we will both help shape tomorrow’s security solution for the IoT (Internet of Things) space.”
In the picture, Professor Kwangjo Kim (left) shakes hands with Marc Bertin, the Chief Technology Officer of Oberthur Technologies (right), after the signing of a memorandum of understanding.
2015.09.24 View 8654 -
 2014 NEREC Conference on Nuclear Nonproliferation: July 31-August 1, 2014, Seoul
The Nonproliferation Education and Research Center (NEREC) at KAIST hosted an international conference on nuclear nonproliferation on July 31-August 1, 2014 in Seoul. The Ministry of Science, ICT and Future Planning, the Korean Nuclear Safety and Security Commission, and the Korea Nuclear Policy Society (KNPS) sponsored the event.
Over one hundred experts and "thought leaders" in nuclear security and nonproliferation attended the conference and discussed issues related to the nonproliferation of nuclear weapons, the role of scientific community in mitigating nuclear threat and promoting the peaceful use of nuclear power, and nuclear disarmament policy.
Keynote speakers were: Steven E. Miller, Director of International Security Program at Belfer Center for Science and International Affairs, Harvard University; Scott D. Sagan, Senior Fellow of the Center for International Security and Cooperation, Freeman Spogli Institute for International Studies, Stanford University; Mark Fitzpatrick, Director of the Nonproliferation and Disarmament Programme, International Institute for Strategic Studies; Sang-Hyun Lee, Director of Security Strategy, Sejong Institute; and Man-Sung Yim, Professor of Nuclear and Quantum Engineering, KAIST.
At the conference, Professor Yim, Director of KAIST NEREC said, “Korea has grown to become a key player in the development of commercial nuclear energy over the past decades. We hope that our conference encourages Korea to be more involved in the efforts of the international community to enhance the global nonproliferation regime.”
2014.08.05 View 16006
2014 NEREC Conference on Nuclear Nonproliferation: July 31-August 1, 2014, Seoul
The Nonproliferation Education and Research Center (NEREC) at KAIST hosted an international conference on nuclear nonproliferation on July 31-August 1, 2014 in Seoul. The Ministry of Science, ICT and Future Planning, the Korean Nuclear Safety and Security Commission, and the Korea Nuclear Policy Society (KNPS) sponsored the event.
Over one hundred experts and "thought leaders" in nuclear security and nonproliferation attended the conference and discussed issues related to the nonproliferation of nuclear weapons, the role of scientific community in mitigating nuclear threat and promoting the peaceful use of nuclear power, and nuclear disarmament policy.
Keynote speakers were: Steven E. Miller, Director of International Security Program at Belfer Center for Science and International Affairs, Harvard University; Scott D. Sagan, Senior Fellow of the Center for International Security and Cooperation, Freeman Spogli Institute for International Studies, Stanford University; Mark Fitzpatrick, Director of the Nonproliferation and Disarmament Programme, International Institute for Strategic Studies; Sang-Hyun Lee, Director of Security Strategy, Sejong Institute; and Man-Sung Yim, Professor of Nuclear and Quantum Engineering, KAIST.
At the conference, Professor Yim, Director of KAIST NEREC said, “Korea has grown to become a key player in the development of commercial nuclear energy over the past decades. We hope that our conference encourages Korea to be more involved in the efforts of the international community to enhance the global nonproliferation regime.”
2014.08.05 View 16006